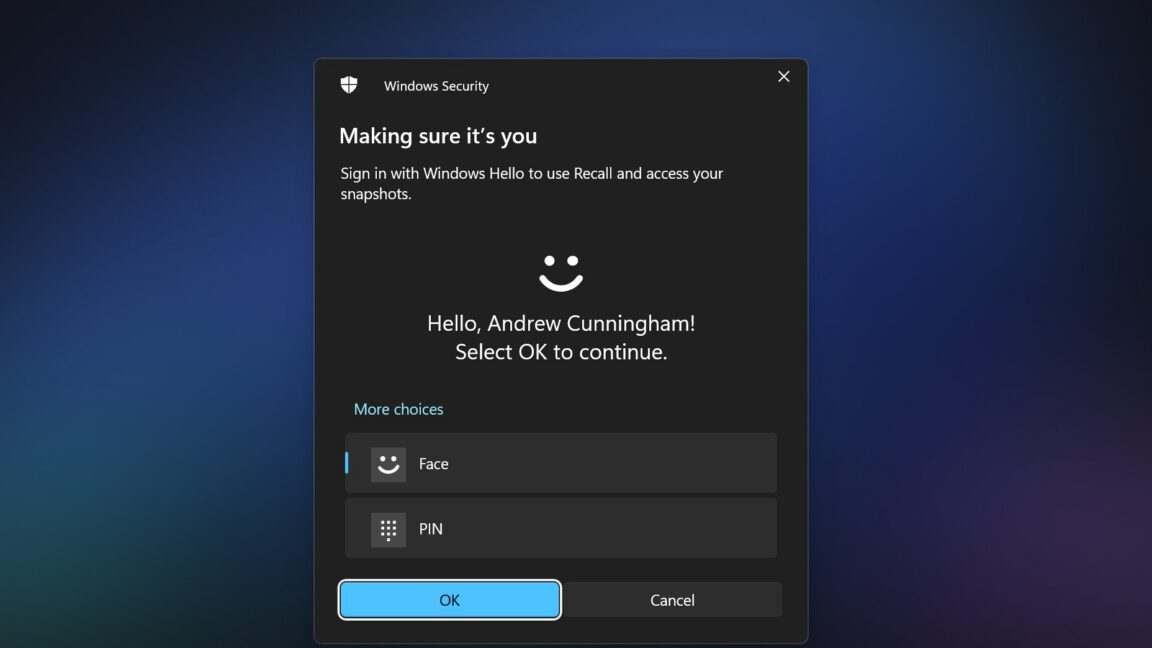
Two years after Microsoft introduced its Copilot+ series of Windows PCs, the Recall feature, designed to track user activity through screenshots, has been scrutinized for its security flaws. Initially, Recall stored user activity in unencrypted files, posing a significant risk to user privacy. Following complaints from journalists and security researchers, Microsoft delayed the feature's launch and made crucial changes, including encrypting locally stored data and requiring Windows Hello for access.
Despite these improvements, security researcher Alexander Hagenah has unveiled a new tool, 'TotalRecall Reloaded', which highlights additional vulnerabilities in the Recall system. While Hagenah acknowledges that the security of the Recall database itself is robust, he points out that the process responsible for delivering Recall data, AIXHost.exe, lacks the same security safeguards.
According to Hagenah, the issue lies not within the Recall database but in how the data is transmitted to AIXHost.exe after user authentication. He states, "The vault is solid. The delivery truck is not." The TotalRecall Reloaded tool exploits this vulnerability by injecting a DLL file into AIXHost.exe, enabling it to capture screenshots, OCR'd text, and other metadata without requiring administrator privileges.
The tool operates in the background, waiting for the user to authenticate via Windows Hello. Once authenticated, it can intercept and store data, even after the Recall session is closed. Moreover, certain actions, such as retrieving the latest Recall screenshot or deleting the Recall database, can be performed without any authentication.
Microsoft's Response: No Bug Found
Microsoft has responded to Hagenah's findings, stating that they do not consider the issue a bug. After reviewing the matter, the company determined that the access patterns reported by Hagenah align with existing security measures and do not represent a security breach. A Microsoft spokesperson commented, "The authorization period has a timeout and anti-hammering protection that limit the impact of malicious queries."
Despite Microsoft's reassurances, the potential for misuse remains. Anyone with access to a user's PC and their Windows Hello fallback PIN can exploit the Recall feature to access sensitive information, including emails, messages, and web activity. While Recall's content filters aim to exclude sensitive financial data, the breadth of information it captures poses serious privacy concerns.
In response to these vulnerabilities, some developers have taken proactive measures. For instance, the Signal Messenger app on Windows has implemented a feature that forces Recall to ignore its content by default, leveraging a flag usually reserved for DRM-protected material. Other applications, such as AdGuard and Brave browser, have introduced similar workarounds to shield users from Recall's data collection.
The ongoing issues surrounding the Recall feature underscore the delicate balance between enhanced functionality and user privacy. As technology continues to evolve, the need for robust security measures becomes increasingly vital in protecting sensitive user data.
Source: Ars Technica News
